★The objective of this guide is to provide a comprehensive review of the security principles with limited scope in terms of information. The primary goal of the software developing team is to use the available information resource to provide and build secure applications for your business and software operations. It could be obtained through the industry-standard implementation of security controls.
★This section specifically focuses on web applications and application infrastructure security, which can be applied on any deployment platform. This checklist is defined to help in developing high-level security elements and helps to overcome common vulnerability scenarios.
★The key factors to consider that client-side controls such as client-based input validation, hidden fields, interface controls upon developing applications.
★An attacker can use a variety of tools to conduct an attack against the applications, flash, java applets, and other client-side objects can be decompiled and analyzed for extensive flaws present in the app. Sometimes, developers feel challenging to discover vulnerabilities due to the scope of the software or programming languages.
Information Collection Techniques:
The Information collection techniques are another integral part of the vulnerability management process, these are the following assessment methodologies that can be performed within an organization to discover a vulnerability, assess, and audit the physical and virtual infrastructure of the network. The industry standard Vulnerability Scanning Tools and controllers are used in this Information and data collection section.
⍟Vulnerability scanning
⍟Web application assessment
⍟Phishing assessment
⍟Network mapping
⍟wireless assessment
⍟Database assessment
⍟Operating system security assessment (OSSA), and
⍟Penetration testing.
Depending on the nature of the Software security flaws, it can be introduced at any stage of the software development lifecycle, including to any or all of the following:
(i) Not identifying security requirements upfront.
(ii) Creating conceptual designs that have logic errors.
(iii) Using poor coding practices that introduce technical vulnerabilities.
(iv) Deploying the software improperly and
(v) Introducing flaws during maintenance or updating.
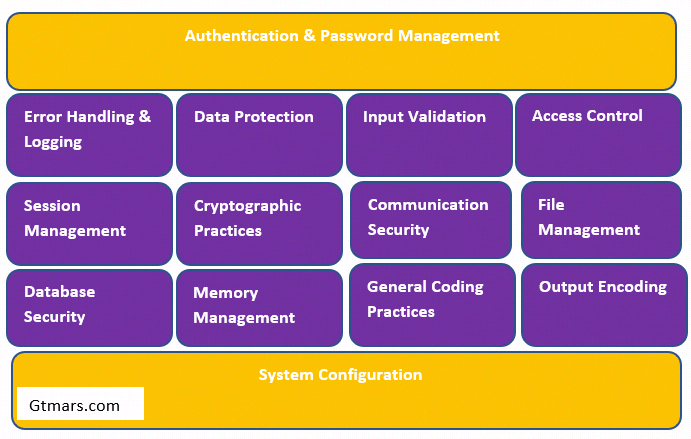
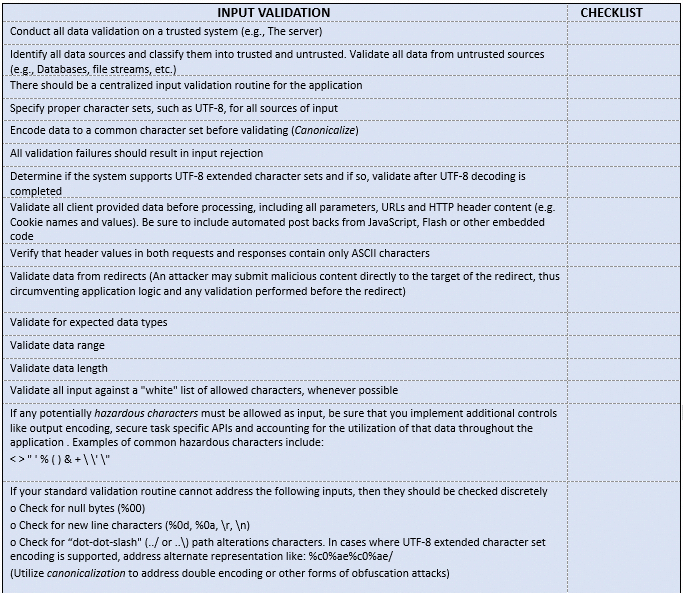
1 Input Validation:
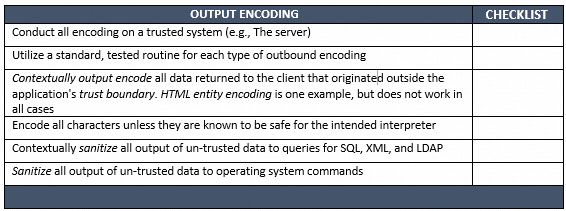
2.Output Encoding:
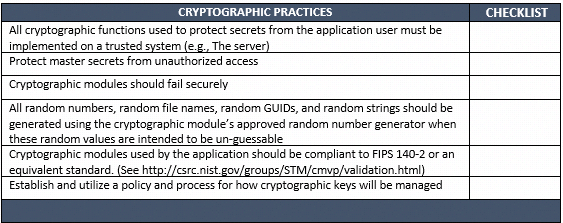
3.Cryptographic Practices:
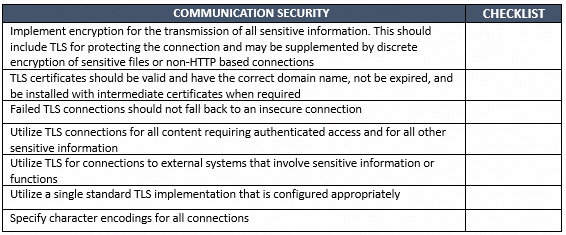
4.Communication Security:
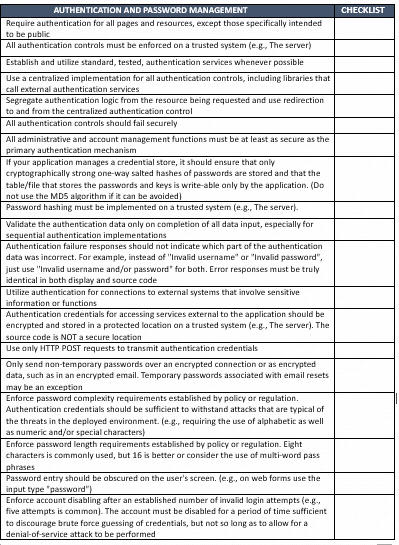
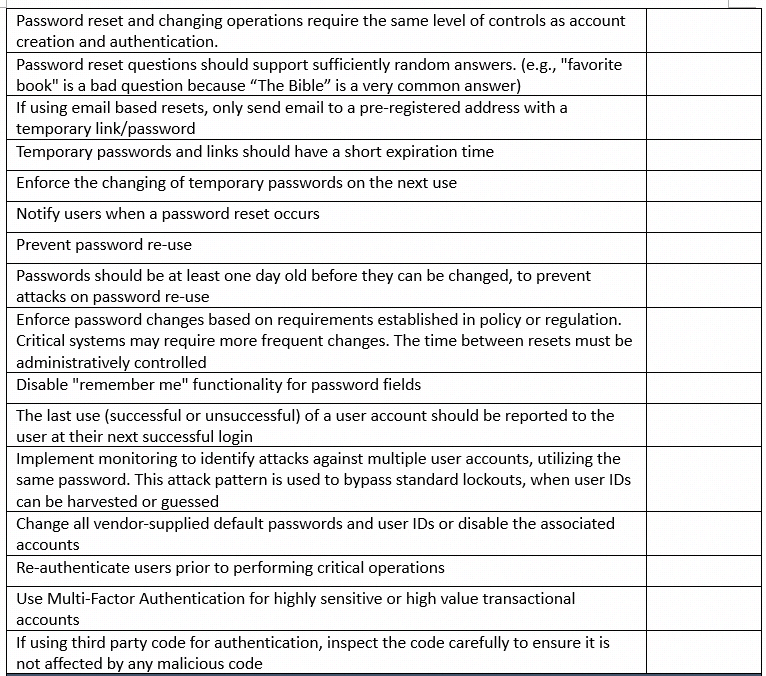
5.Authentication and Password Management:
6.Session Management:

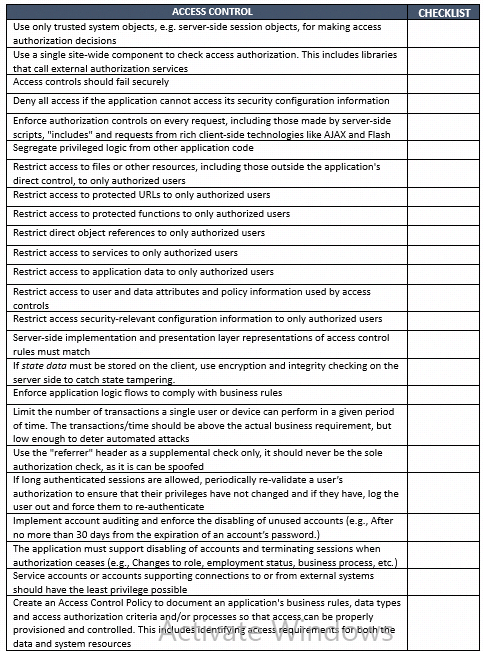
7. Access Control:
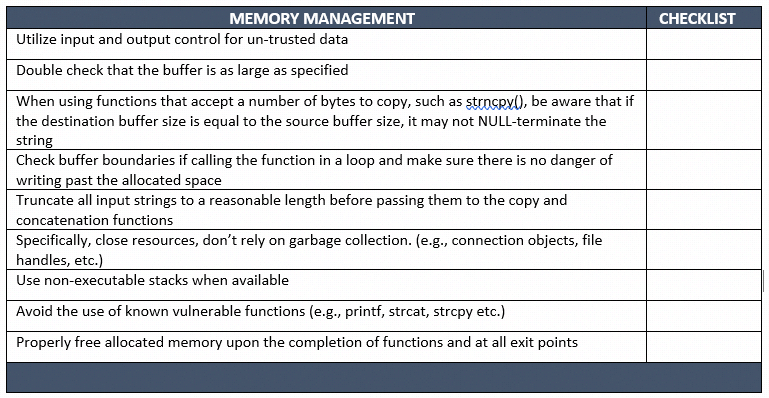
8. Memory Management:
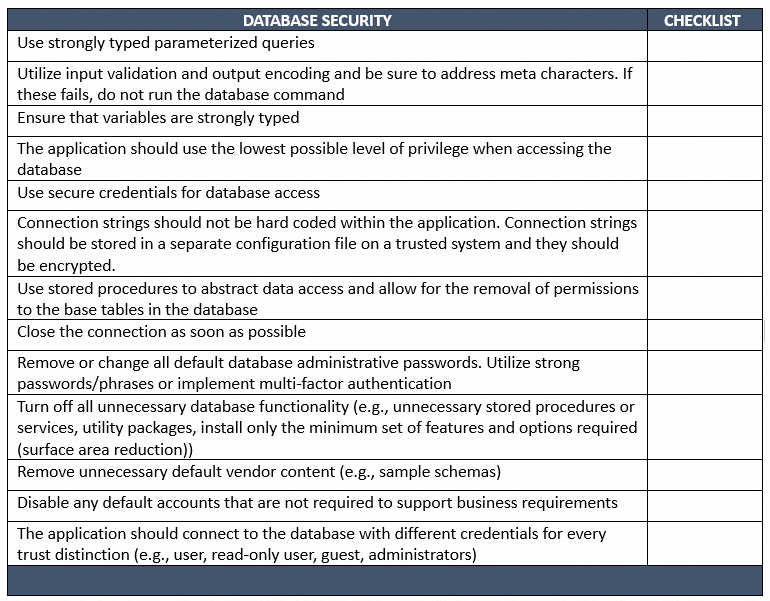
9. Database Security:
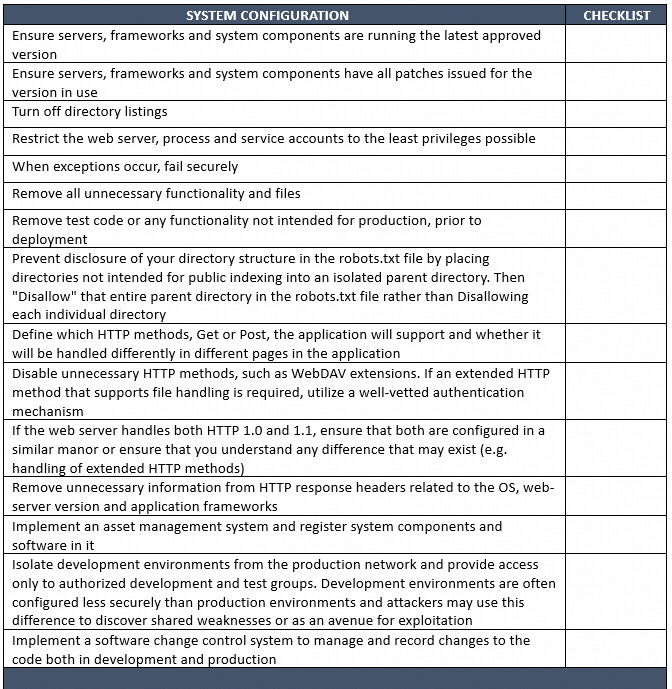
10. System Configuration:
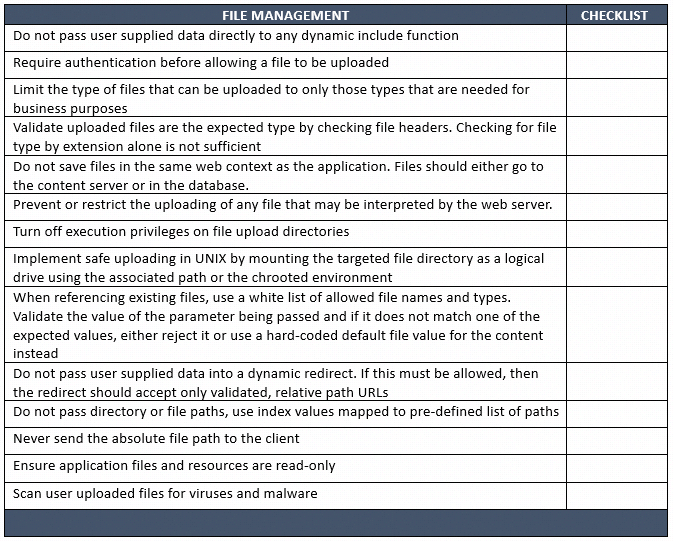
11. File Management:
12. Error Handling and Logging:

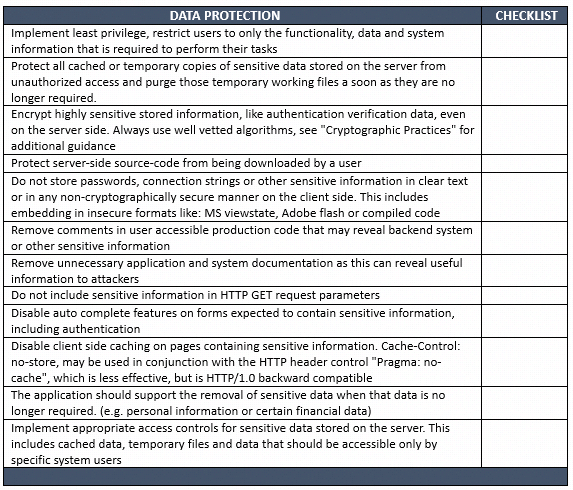
13. Data Protection:
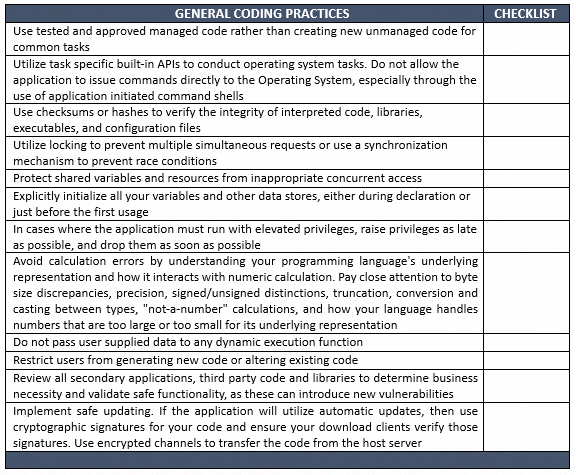
14. General Coding Practices:
Conclusion:
★The public and private sector organizations integrate a vulnerability management framework and secure coding practices successfully into their program to ensure a smooth onboarding and development of any software applications. It helps to identify, defend against any threats, and emerging vulnerability. Deploying a VMF is all about managing risk, it allows to locate the risk and remediate the required solution to reduce the risk further causing damage to the IT system or its applications. The technical objectives can be met by deploying industry-recommended tools to perform vulnerability scanning. Finally, an appropriate set of measures, and controls to be taken when defining your scope for successful results in the software development life cycle (SDLC).
Refer further to understand how to integrate risk management into SDLC.
What Is Risk Management And How To Integrate It Into SDLC: Best Explanation Ever
Quick Reference: OWASP
— — — — — — — — — — — — — -THE END — — — — — — — — — —
Feel free to get in touch with us for any inquiries :
Follow my tech blog to get weekly feeds :
https://hackernoon.com/u/gtmars.com
https://gtmars.medium.com/
Space and Mars Colonization Website: https://gtmars.com
Free travel itinerary planning Website: plan2trip.com



















No comments:
Post a Comment